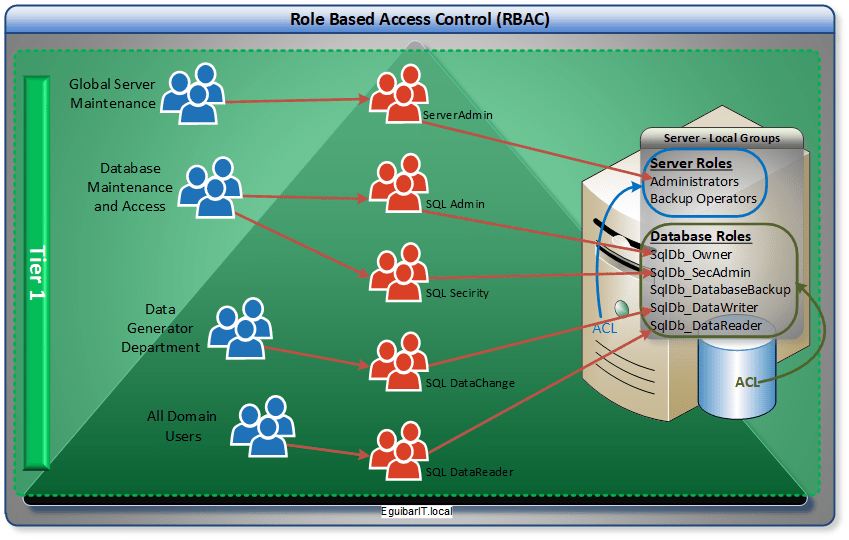
Role Based Access Control (RBAC) with Spring Boot and JWT | by Imesha Sudasingha | Geek Culture | Medium
Role Based Access Control Ppt Powerpoint Presentation Styles Outfit Cpb | Presentation Graphics | Presentation PowerPoint Example | Slide Templates

An enhancement of the Role-Based Access Control model to facilitate information access management in context of team collaboration and workflow - ScienceDirect







.png?width=687&name=RBAC_blog_diagram%20(2).png)